Unraveling the Threat of Code Tampering: Safeguarding Digital Fortresses
Introduction
In the rapidly evolving landscape of digital technology, the integrity of code is paramount. Code tampering, a malicious practice where unauthorized alterations are made to a software’s source code or binaries, poses a significant threat to the security and functionality of applications. As our reliance on digital platforms grows, understanding the nuances of code tampering becomes crucial for developers, businesses, and end-users alike.
Understanding Code Tampering
Code tampering, also known as code injection or code meddling, involves unauthorized alterations to the source code or binaries of a software application. Malicious actors may exploit vulnerabilities in the code to introduce changes with the intent of compromising the security, functionality, or integrity of the software. This can lead to a range of adverse consequences, including data breaches, unauthorized access, and the deployment of malware.
Types of Code Tampering
1. Source Code Tampering
Source code tampering involves unauthorized modifications to the source code of an application. Malicious actors may gain access to the source code through various means, such as insider threats or exploiting vulnerabilities in the development environment.
2. Binary Code Tampering
Binary code tampering occurs when attackers manipulate the compiled binaries of an application. This can involve altering the executable files or injecting malicious code directly into the binaries, compromising the integrity of the software.
3. Runtime Code Tampering
Runtime code tampering involves making alterations to the code while the application is running. Attackers may use techniques like hooking, patching, or memory manipulation to modify the behavior of the software at runtime.
Implications of Code Tampering
The ramifications of Anti code tampering are far-reaching and can have severe consequences for individuals, businesses, and even entire industries.
1. Security Breaches
Code tampering can be a gateway for cybercriminals to breach the security of an application. By injecting malicious code, attackers can exploit vulnerabilities, gain unauthorized access, and compromise sensitive data.
2. Data Manipulation
Malicious alterations to code can result in the manipulation of data within an application. This could lead to inaccurate information, financial losses, and damage to the reputation of the affected entity.
3. Intellectual Property Theft
Source code is often a valuable intellectual property asset for software developers and companies. Code tampering poses the risk of intellectual property theft, as attackers may seek to steal, replicate, or use proprietary code for their purposes.
Common Attack Vectors
Understanding the common ways in which code tampering occurs is essential for developing effective strategies to mitigate these threats.
1. Reverse Engineering
Attackers often employ reverse engineering techniques to analyze and understand the functioning of an application. Once they comprehend the logic and structure of the code, they can identify vulnerabilities and weaknesses that can be exploited for tampering.
2. Man-in-the-Middle Attacks
Man-in-the-middle (MitM) attacks involve intercepting communication between two parties. In the context of code tampering, attackers may alter the code during transmission, leading to compromised integrity when it reaches the end-user.
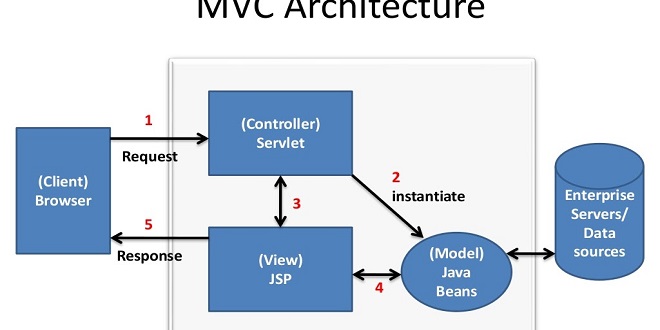
3. Insecure APIs
Application Programming Interfaces (APIs) are potential weak points that can be exploited for code tampering. Insecure APIs may allow attackers to manipulate data, inject malicious code, or compromise the overall security of an application.
Safeguarding Against Code Tampering
Protecting against code tampering requires a multi-faceted approach that encompasses secure coding practices, robust architecture, and continuous monitoring.
1. Code Obfuscation
Code obfuscation involves transforming the source code or binaries to make it difficult for attackers to understand and reverse engineer. This hinders the process of code tampering by increasing the complexity of the code.
2. Secure Coding Practices
Developers play a crucial role in preventing code tampering through the implementation of secure coding practices. This includes regular code reviews, input validation, and adherence to security best practices during the development lifecycle.
3. Code Signing
Code signing involves digitally signing executables or scripts to verify their authenticity. This helps ensure that the code has not been tampered with and comes from a trusted source. Code signing is particularly crucial for software updates.
4. Runtime Protection
Implementing runtime protection mechanisms can detect and prevent code tampering during the execution of an application. This may involve the use of integrity checks, code integrity verification, and monitoring for abnormal behavior.
5. Encryption
Encrypting sensitive data within the application and during transmission adds a layer of security. Even if attackers manage to tamper with the code, encrypted data remains protected, reducing the impact of potential breaches.
Emerging Technologies and Code Tampering
As we navigate the ever-changing landscape of technology, innovations also bring new challenges. Emerging technologies such as the Internet of Things (IoT), artificial intelligence, and blockchain introduce additional considerations when it comes to code tampering.
1. IoT Vulnerabilities
The proliferation of IoT devices introduces a vast attack surface, making them susceptible to code tampering. Malicious actors may exploit vulnerabilities in device firmware, compromising the functionality and security of these interconnected devices.
2. AI Algorithm Security
Machine learning and AI algorithms rely heavily on code integrity. Tampering with the underlying algorithms can result in biased outputs, unauthorized access to sensitive data, or manipulation of decision-making processes. Ensuring the security of AI code is crucial for responsible and ethical deployment.
3. Blockchain Integrity
While blockchain is renowned for its tamper-resistant nature, smart contracts and decentralized applications (DApps) can still be vulnerable to code tampering. Securing the codebase of smart contracts is imperative to prevent unauthorized changes that could compromise the integrity of blockchain-based systems.
Regulatory Compliance and Code Tampering
In an era where data privacy and security regulations are becoming increasingly stringent, code tampering can have legal implications. Organizations must not only protect against code tampering for the sake of data integrity but also comply with various regulatory frameworks.
1. GDPR Compliance
The General Data Protection Regulation (GDPR) mandates the protection of personal data. Code tampering incidents that lead to data breaches can result in severe penalties. Implementing robust code security measures is, therefore, a critical component of GDPR compliance.
2. Industry-Specific Regulations
Various industries, such as finance, healthcare, and telecommunications, have their own set of regulations governing data security. Code tampering can lead to non-compliance with these regulations, exposing organizations to legal consequences and reputational damage.
Conclusion
The future holds both challenges and opportunities in the ongoing battle against code tampering. By staying informed, adopting innovative technologies, and fostering a culture of cybersecurity resilience, we can build a digital landscape that is robust, secure, and resistant to the insidious attempts of those seeking to compromise the integrity of our code. As guardians of the digital realm, commitment to code security will shape the future of a safer and more resilient technological ecosystem.